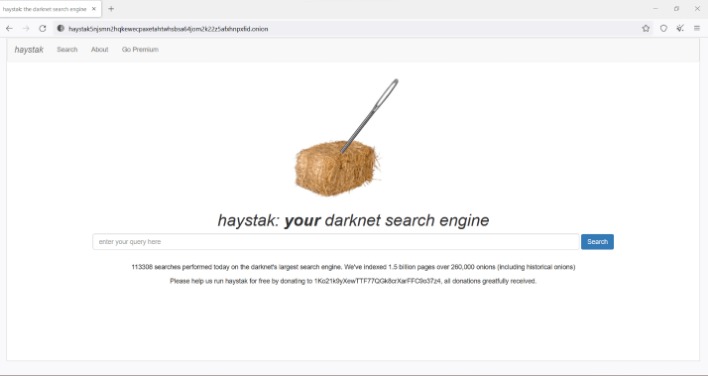
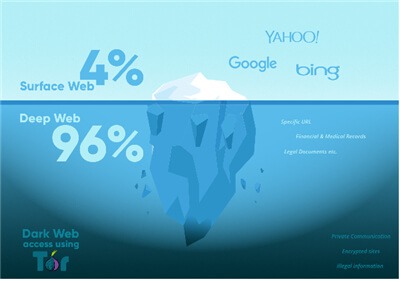
To access them, copy and paste the hyperlinks provided into the Tor browser. If you’ve ever experienced an uptick in phishing attacks and spam after a data leak or breach, it may be because your personal information has been posted to the dark web. Unfortunately, many dark web websites are devoted to the illegal trade of leaked personal information. On the dark web, traffic is routed through multiple server nodes that don’t log activity, obscuring the user’s origin and enabling anonymous communication.
The most active marketplace in terms of number of users and traded volume is AlphaBay, followed by Hydra. Out of the 31 marketplaces, 3 are marketplaces dedicated to fake and stolen IDs and credit cards. Out of the selected marketplaces, 12 were subject to an exit scam, 9 were raided, 3 were voluntarily closed by their administrators, and 7 are still active. In order to gain information on the analysed marketplaces, we collected additional data from the Gwern archive on dark marketplace closures1. Our dataset includes transactions between addresses belonging to a dark marketplace (in red) and its nearest neighbours (in black), as well as the transactions between nearest neighbours and “other” Bitcoin addresses (in grey).
The darknet has long been known for its clandestine markets, where a variety of goods and services are exchanged away from the watchful eyes of traditional law enforcement. As we move into 2026, the landscape of active darknet markets continues to evolve rapidly, driven by advancements in technology and changing patterns of user behavior. This article aims to provide insight into what makes these markets tick, the types of activities occurring within them, and how they are anticipated to change in the near future.
Active Darknet Markets 2026
The year 2026 presents a unique turning point for active darknet markets. Recent trends suggest a combination of resilience and adaptation among these platforms in response to law enforcement crackdowns and changes in user preferences.
We at KELA help you move beyond basic dark web monitoring by providing real-time, contextualized intelligence from the cybercrime underground that focuses specifically on threats targeting your organization. Provides detailed technical and metadata information The open-source setup also allows analysts to adapt it for their own research systems. This makes it a powerful tool for tracking infrastructure or investigating network relationships between hidden services. It doesn’t just find pages — it gathers technical data such as uptime, bitcoin addresses, SSH keys, and service fingerprints. Delivers high-quality, relevant search results
- The coordinated global law enforcement effort targeting the ‘ShinyHunters,’ ‘Hollow,’ ‘Noct,’ and ‘Depressed’ personas followed the February arrest of Kai West (also known as ‘IntelBroker’), who previously administered BreachForums.
- Aged datasets are still sold, but typically at lower prices and used for low-effort attacks like broad credential stuffing.
- Recent research on attributing anonymised Bitcoin addresses to named entities18,19,20,21 has not yet been applied to the investigation of the dynamics of dark marketplaces.
- DuckDuckGo is a privacy-focused search engine that works as Tor browser’s primary search engine.
- At Market.us Scoop, we strive to bring you the most accurate and up-to-date information by utilizing a variety of resources, including paid and free sources, primary research, and phone interviews.
- As of 2026, estimates suggest there are roughly 30,000 active dark web sites, commonly referred to as hidden or “.onion” services.
Characteristics of Current Darknet Markets
- Increased Anonymity: Many users are now employing enhanced privacy measures, such as VPNs and encrypted communications, making it harder to track their activities.
- Diverse Offerings: While illicit goods like drugs and weapons remain prevalent, markets are increasingly selling digital products, including hacking services and stolen data.
- User Reviews and Ratings: Most platforms have integrated review systems to help buyers gauge the reliability of sellers.
- Decentralized Platforms: New technologies like blockchain are enabling decentralized markets, reducing the risk of shutdowns by authorities.
Types of Goods and Services on Active Darknet Markets
Among the offerings on these platforms, you will find:
- Many modern security frameworks now emphasize monitoring external threat environments, including underground forums and leak sites.
- This distribution reflects how closely the dark web economy is tied to data breaches and cybercrime.
- These tools continuously scan criminal marketplaces and private forums that search engines can’t access.
- Since the year 2000, some of the emerging cyber-arms industry operates online, including the Eastern European "Cyber-arms Bazaar", trafficking in the most powerful crimeware and hacking tools.
- In the first arc of the anime series Lupin the 3rd Part V, Lupin III steals digital currency from the "Marco Polo" darknet market.
- Second, while wholesale drug purchasing revenues have steadily climbed since that drop, they have yet to regain their former highs.
- Illegal Substances: A vast array of drugs continues to be the hallmark of darknet markets.
- Weapons and Ammunition: These markets often feature an alarming variety of firearms and ammunition.
- Stolen Data: Personal data, financial information, and hacked accounts are frequently traded.
- Fraud Services: Services that help facilitate scams and include money laundering options.
Future Trends in Darknet Markets
As we look ahead, several trends are likely to shape the future of active darknet markets:
- Regulatory Pressures: Increased scrutiny and regulation by governments may push markets underground, leading to a rise in private forums.
- Technological Enhancements: The continual advancement in encryption and anonymity tools will elevate the difficulty for authorities to monitor these platforms.
- Community-Driven Security: Markets that foster a strong community ethos are anticipated to thrive, as trust among users becomes critical.
FAQs about Active Darknet Markets
- Are darknet markets legal?
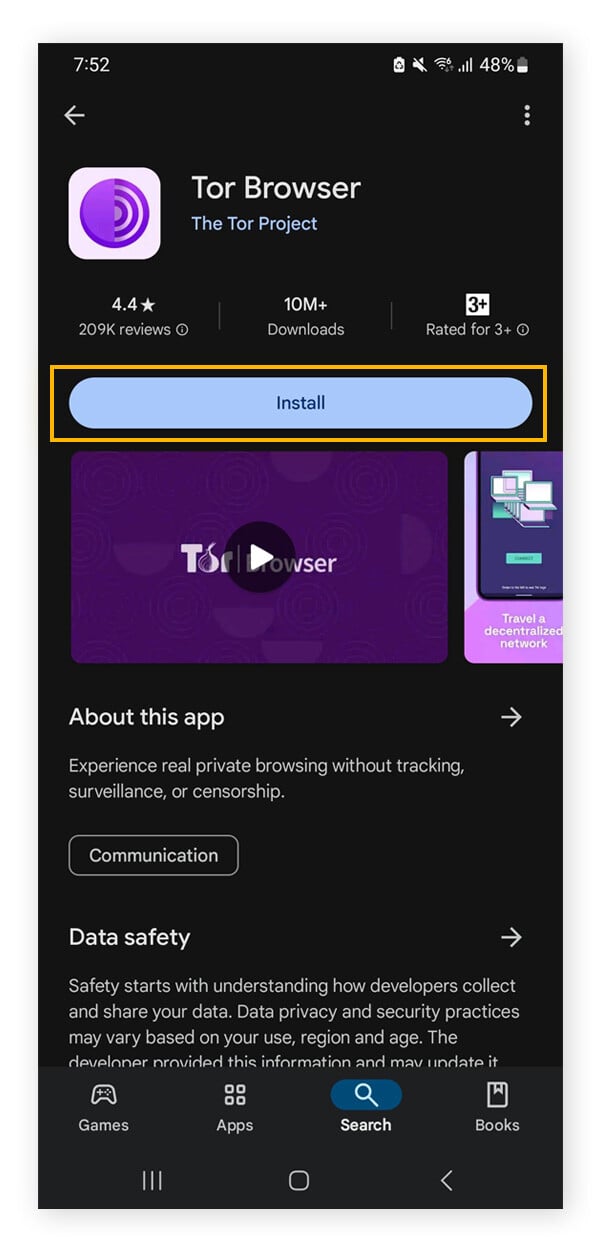
While merely accessing the darknet is legal, participation in illegal activities, such as purchasing illicit goods, is against the law. - How do I access darknet markets?
Typically, users require specialized software like Tor to access these hidden networks. - What should I be cautious of when browsing?
Be aware of potential scams, malware, and the legal implications of engaging in illicit activities. - Can I remain anonymous on the darknet?
While tools exist to enhance anonymity, no method is foolproof; vigilance is always required.
Understanding the dynamics of active darknet markets in 2026 is crucial for fostering informed discussions about cybersecurity, law enforcement challenges, and personal safety. As these markets continue to adapt and evolve, staying educated about their implications can empower individuals and communities to navigate this complex digital landscape responsibly.