The darknet market has gained significant attention in recent years, often shrouded in mystery and intrigue. Many people are curious about what it is, how it functions, and the potential implications of accessing such underground spaces. Understanding the darknet market is crucial for anyone looking to navigate the online world safely and wisely. This article aims to provide a comprehensive overview of what accessing the darknet market entails, how it works, and the necessary precautions to take to ensure security and anonymity.
In addition, encrypted messaging platforms like Telegram and QQ provide a safe haven for communications about malicious acts and are, therefore, popular among threat actors. Most Dark Web users use the TOR browser, which is designed to make the Dark Web easier to navigate. Darknets are encrypted overlay networks that sit on top of the public Internet. The Onion Router (TOR) technology used by the TOR browser and the Dark Web was created by a project funded by the US Naval Research Lab (NRL).
Accessing Darknet Market
The darknet is a part of the internet that isn't indexed by traditional search engines. It requires specific software and configurations to gain entry. Below is a guide to help you understand how to access the darknet market safely:
1. Understanding the Darknet
- The darknet is often confused with the deep web, which includes all parts of the web not indexed by search engines.
- While the deep web contains benign content such as databases and private websites, the darknet is specifically used for illicit activities, providing a sense of anonymity.
2. Tools Needed for Access
Accessing the darknet market typically requires specific tools:
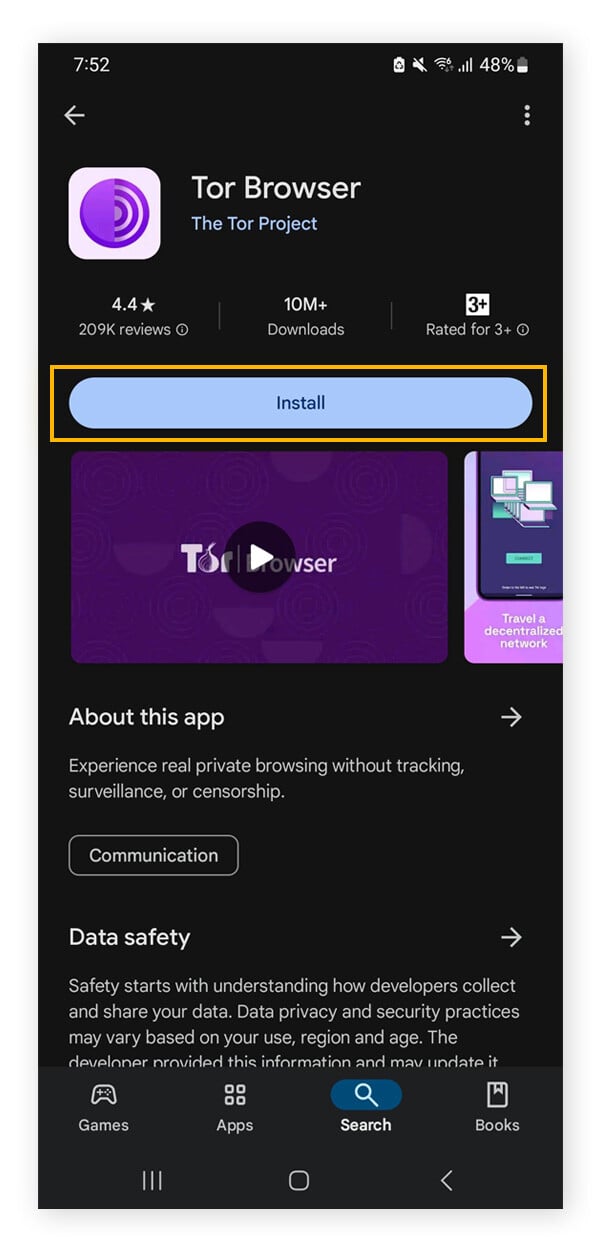
- Tor Browser: This is the primary software used to access .onion sites, allowing users to browse anonymously.
- VPN (Virtual Private Network): A VPN is recommended for an added layer of security and privacy by masking your IP address.
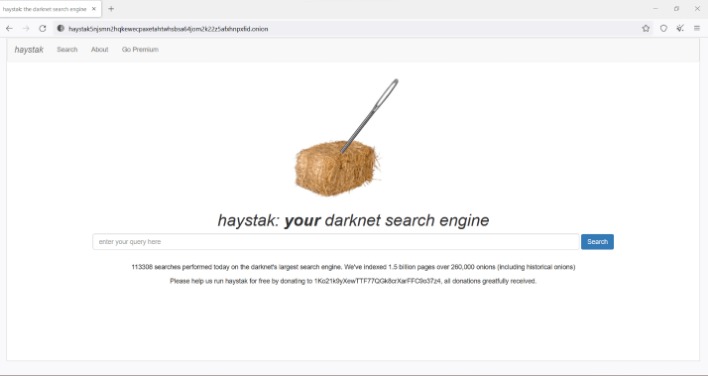
3. Finding Darknet Marketplaces
Once equipped with the necessary tools, users can search for darknet marketplaces. Here are some tips:
- Join forums or communities that discuss the darknet; these can provide valuable information and market links.
- Use reputable sources to gather information, as many marketplaces are scams or fraudulent.
4. Safety Precautions
Before accessing the darknet market, consider the following precautions:
- Never share personal information or cryptocurrency wallets linked to your identity.
- Use a fresh virtual machine setup for increased security.
- Stay aware of potential scams and the risks associated with your activities.
- State-sponsored threat actors are cybercriminal groups supported or directly managed by government agencies on the darkweb market.
- After your data is secured inside multiple layers of encryption, your web traffic is transmitted through a series of network nodes, called onion routers.
- Any device you use to connect to the internet has one.
- Table 3 provides an overview of selected dark web markets’ account security mechanisms implementation.
- The admins would periodically release massive dumps of stolen cards for free on hacking forums to promote the site.
5. Legal and Ethical Considerations
Accessing the darknet also comes with legal implications:
- Engaging in illegal activities, such as buying drugs or weapons, can result in severe legal consequences.
- Educating oneself about the ethical ramifications of accessing such markets is essential.
FAQs
Q: Is accessing the darknet illegal?
A: Accessing the darknet itself is not illegal; however, many activities conducted there may be against the law.
Q: Can my identity be traced on the darknet?

A: While the darknet is designed to enhance privacy, it is still possible to be traced if sufficient precautions are not taken.
Q: What should I do if I encounter illegal content?
A: It is advisable to exit the site immediately and report it to relevant authorities if you feel comfortable doing so.
In conclusion, understanding the intricacies of the darknet market is essential for making informed choices. While curiosity about this hidden part of the internet is common, being aware of the associated risks and responsibilities is crucial for maintaining security and legality in the digital age.