In an era where digital privacy and anonymity are becoming increasingly important, many users are curious about the mechanisms of the internet's less visible side—the darknet. Accessing the darknet can be daunting, particularly on mobile devices like the iPhone. However, with proper knowledge and precautions, users can navigate this complex landscape safely. This article will guide you on how to access darknet on iPhone while prioritizing your security and anonymity.
Access Darknet On Iphone
Before diving into the steps needed to access the darknet on your iPhone, it's vital to understand what the darknet is and its significance.
- We continually track down and add new data brokers and people search sites to our list, so your level of protection keeps improving over time.
- Given the prevalence of malware across the dark web, it’s vital to have antivirus software installed and active on your device when accessing it.
- Anything beyond that index, which is hidden behind a password or any software, is known as Deep Web or Dark Web.
- Lots of criminal activity happens on the Dark Web because it offers the anonymity that enables hackers and scammers to go undetected — but only up to a certain point.
- In 2022, Kaspersky researchers found that when looking up "Tor Browser" in Chinese on YouTube, one of the URLs provided under the top-ranked Chinese-language video actually pointed to malware disguised as Tor Browser.
- The same goes for the different pages that pop up in webmail services, like Gmail, or academic databases on a university network.
These nefarious tools allow hackers to guess thousands, even millions, of password combinations per second. "Understand that the web as we know it today is privacy-hostile and that nothing is foolproof, do research, support organisations and projects — like Tor Project, i2p, and Open Privacy — that are building and maintaining tools that make enforcing your consent easier." It's still possible to track someone's traffic pinging through the Tor nodes, though it is difficult. With any security and privacy issue, it's about your threat model, which is simply what attacks or invasions you're actually worried about. "Contrary to what most people think, these modes do not actually protect your privacy," she says. Once you've downloaded and installed the Tor browser, you can browse just as you would your usual browser, but Muffett offers a caveat to avoid unencrypted sites — those with only "http" in the URL rather than "HTTPS".
What is the Darknet?
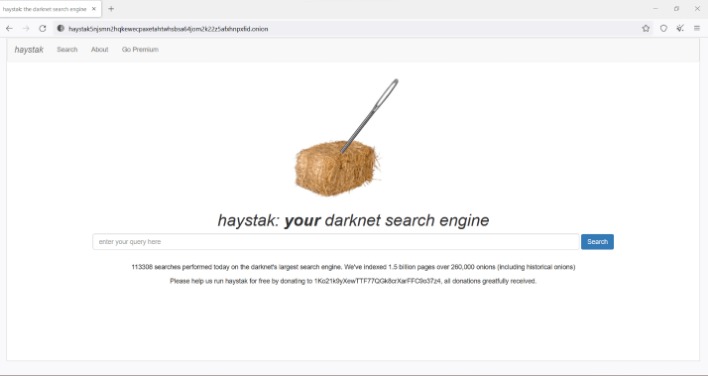
The darknet is a part of the internet that is not indexed by traditional search engines. It requires specific software and configurations to access. Often associated with anonymity, it hosts various forums, marketplaces, and hidden services. While it can serve noble purposes, such as promoting free speech in oppressive regimes, it is also home to illegal activities.
Users can find forums, blogs, and websites discussing various subjects, often with greater anonymity than on the surface web. By combining a reliable password manager with these best practices, users can significantly enhance their overall digital security. It's crucial to prioritize strong security practices, such as using a unique and complex master password and setting up secure recovery options.
This would allow the adversary to simultaneously know the onion service involved in the request, and the IP address of the client requesting it (where the requesting client could be a visitor or owner of the onion service). Because traffic from all Tor users is shared by a comparatively small number of exit relays, tools can misidentify distinct sessions as originating from the same user, and attribute the actions of a malicious user to a non-malicious user, or observe an unusually large volume of traffic for one IP address. Tor's architecture for deciding the consensus relies on a small number of directory authority nodes voting on current network parameters. For Tor, these include network parameters like which nodes are good and bad relays, exits, guards, and how much traffic each can handle.
Steps to Access Darknet on iPhone
To securely access the darknet on your iPhone, follow these steps:
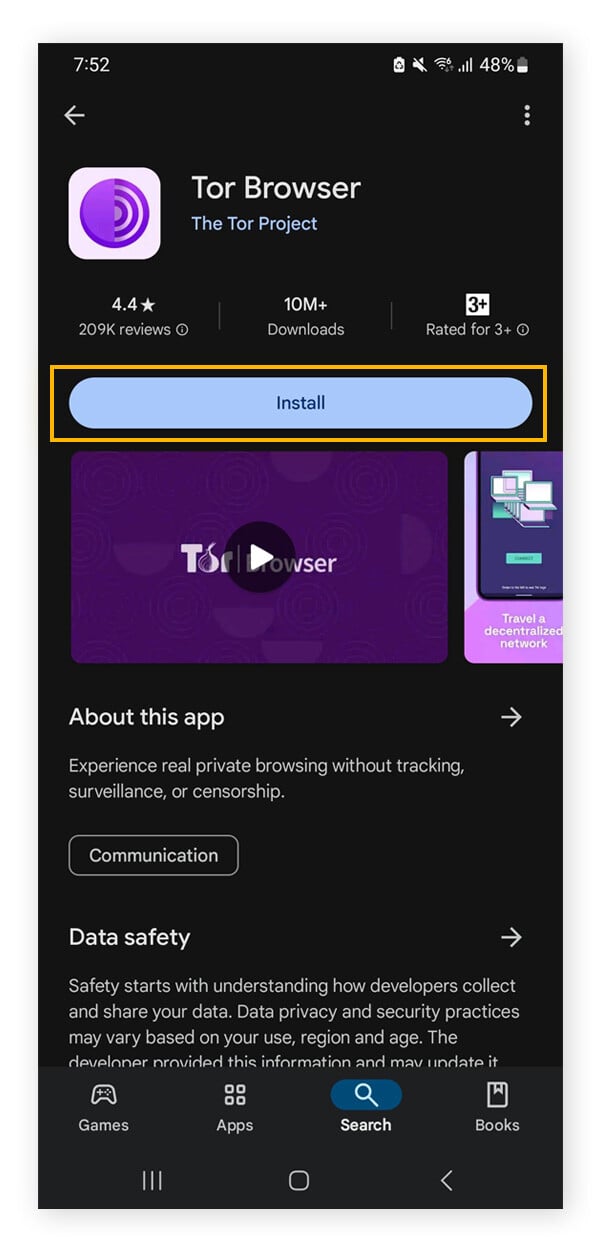
- Download a Tor Browser: The primary method to access the darknet is through the Tor network. Look for reputable Tor browser applications compatible with iOS.
- Install a VPN: To enhance your privacy and security, consider using a Virtual Private Network (VPN) before connecting to the Tor network. This adds an extra layer of security by masking your IP address.
- Configure the VPN: After installing your VPN, ensure that you configure it correctly. Select a server location that maintains strong privacy policies.
- Open the Tor Browser: Launch the Tor browser application you downloaded. Follow any prompts to establish a connection to the Tor network.
- Start Exploring: Once connected, you can access .onion websites. Be cautious and stay informed about potential risks and scams.
Precautions to Take
When navigating the darknet, it’s crucial to prioritize your safety. Consider the following precautions:
- Avoid sharing personal information.
- Ensure your software and apps are always up to date.
- Be wary of links or files from untrusted sources.
- Regularly clear your browser cache while using the Tor browser.
FAQs
Is it legal to access the darknet on my iPhone?
Accessing the darknet itself is not illegal, but engaging in unlawful activities while on it is. Always ensure you are aware of the laws in your jurisdiction.
Can using a VPN guarantee my anonymity on the darknet?
A VPN significantly enhances your privacy but does not guarantee complete anonymity. Always use a combination of tools and take proactive security measures.
What should I do if I encounter illegal content?
If you come across any illegal activities, it is best to exit the site immediately and consider reporting it to the appropriate authorities.
By understanding how to access darknet on iPhone with safety and responsibility, you can navigate this hidden world while protecting your identity and personal information. Always stay informed and exercise caution as you explore the depths of the darknet.