Tor Browser both anonymizes and encrypts your location through onion routing, better protecting your data when you get on the dark web. While proxies replace your IP address and location, they don't encrypt internet traffic, meaning your data is still exposed in transit. A proxy server acts as an intermediary between you and host services, while Tor is an encrypted network of decentralized servers. Tor uses onion routing to encrypt and reroute web traffic through Tor’s onion network. With an encrypted and anonymous connection, Tor helps you access the unindexed part of the internet known as the dark web. This helps automate alerting, enrich existing intelligence, and reduce the manual effort involved in tracking threat actors.
Access top incident response plan templates for your security team, find out which are cloud native, and learn how you can respond faster to minimize damage. Monitor for privilege escalation attempts and unusual permission usage patterns. Use Cloud Infrastructure Entitlement Management (CIEM) to identify over-privileged accounts—for example, developers with production admin rights when they only need read access to dev environments.
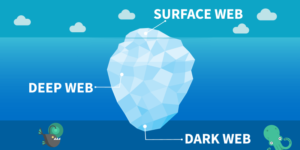
The dark web conjures images of anonymity, secrecy, and hidden knowledge. While it is often portrayed as a risky terrain, understanding how to access it can be crucial for safeguarding privacy and promoting digital literacy. This article aims to provide a comprehensive overview of accessing the dark web, shedding light on its workings and potential uses, all while ensuring that information is conveyed for educational purposes only.
Accessing Dark Web
The dark web is a part of the internet not indexed by traditional search engines, requiring specific software to access. Most people associate the dark web with illegal activities; however, it also houses forums, information-sharing platforms, and resources that can be beneficial. Here’s how to navigate this hidden digital landscape safely.
What You Need to Access the Dark Web
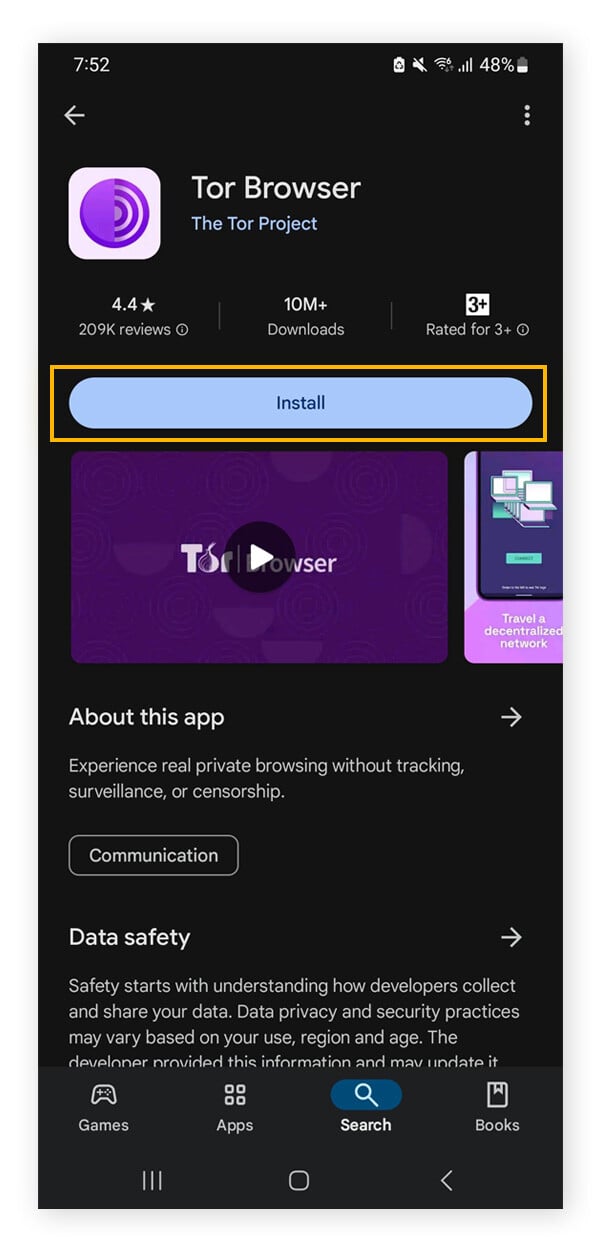
- Specialized Browser: The most common way to access the dark web is by using Tor (The Onion Router). This browser routes internet traffic through multiple servers, anonymizing the user's activity.
- VPN (Virtual Private Network): Utilizing a VPN adds an extra layer of security by encrypting your internet connection, further protecting your identity.
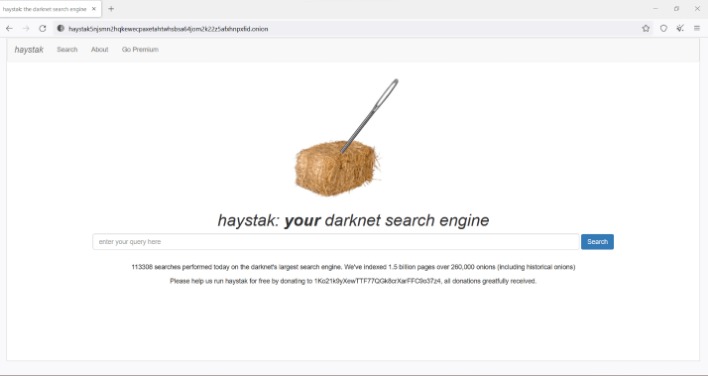
- Knowledge of Dark Web Addresses: Unlike the surface web, dark web sites often use .onion domains. These addresses are not found through standard search engines, but can be found in directories or forums specialized in dark web resources.
Steps to Access the Dark Web
- Download and install the Tor browser from the official website.
- Consider setting up a reputable VPN service to secure your connection.
- Launch the Tor browser and connect to the Tor network.
- Enter .onion addresses directly or browse through dark web directories to find links to websites.

Staying Safe While Accessing the Dark Web
Accessing the dark web comes with risks, and it’s essential to prioritize your safety:
- Avoid Sharing Personal Information: Never disclose personal details, including names, addresses, and financial information.
- Be Wary of Downloads: Files and links circulating on the dark web can contain malware; exercise caution before clicking and downloading.
- Stay Informed: Familiarize yourself with current threats and practices for safe browsing.
- Because of the nature of the dark web, it’s naturally home to more threatening actors.
- Initial work on the dark web began in 2000 by University of Edinburgh student Ian Clarke, who created the "Distributed Decentralised Information Storage and Retrieval System."
- In the 1990s, as internet usage grew, people became worried about their privacy and safety.
- This is because dark web browsers tend to focus more on security features than on improving web technologies and use different methods to ensure these.
Common Uses of the Dark Web
While it's known for its illicit side, there are legitimate uses for the dark web, including:
- Whistleblower Platforms: Websites like SecureDrop allow individuals to share sensitive information securely.
- Privacy-Focused Discussions: Various forums provide safe spaces for political activists, journalists, and individuals living under oppressive regimes.
- Cryptocurrency Transactions: The dark web often uses cryptocurrencies for transactions, promoting anonymity in financial dealings.
FAQs about Accessing the Dark Web
Q: Is accessing the dark web illegal?
A: Accessing the dark web itself is not illegal; however, engaging in illegal activities while there is against the law.
Q: Can I be tracked while on the dark web?
A: Although the Tor network offers anonymity, no system is foolproof. Using a VPN enhances your security, but remain vigilant about sharing information.
Q: What are some legitimate websites on the dark web?
A: Numerous resources for education and privacy exist on the dark web, including forums, libraries, and news outlets focusing on whistleblowing and activism.
Understanding how to access the dark web responsibly can empower individuals to seek information and connect in ways that promote privacy and knowledge. With the right tools and precautions, users can navigate this hidden part of the internet safely and informedly.