Please reboot your device and if the issue persists, visit keepersecurity.com/support for assistance. Check whether your credentials have been exposed in a data breach and are circulating on the dark web with Keeper’s free dark web scan. Excluding the fraction of the Deep Web referred to as the “Dark Web,” browsing the Deep Web is like browsing the Surface Web, and comes with the same concerns regarding your privacy and security. Web crawlers don’t enter words into input fields like search boxes, so they may never get to this material. A website may have lots of material that’s located by searching for a keyword (e.g. on the example.com blog).
Because Tor bounces a user's information to servers all over the world before delivering it, someone monitoring a website might read an American user as someone from any nation. Tor functions by automatically encrypting all data the user is sending and receiving, then bouncing that data through Tor servers located around the world. Common software packages used for this purpose include I2P, Freenet, and The Onion Router (Tor). Because the Dark Web is sometimes used for illicit activities, it receives far more publicity than the rest of the Deep Web.
- It’s designed to allow users to browse and communicate anonymously.
- Law enforcement agencies worldwide have grappled with the challenges posed by the Dark Web, attempting to balance the need for online privacy with the necessity of combating criminal activities.
- Want to stay informed on the latest news in cybersecurity?
- When exploring the dark web, it’s crucial to exercise caution, as it’s not devoid of risks.
- When investigating online suspects, police typically use the IP (Internet Protocol) address of the individual; however, due to Tor browsers creating anonymity, this becomes an impossible tactic.
- Finally, note that—despite some negative connotations with the name—it’s generally a good thing that much of the content we access online is on the Deep Web.
The dark web is a part of the internet that is not indexed by traditional search engines. While it may conjure images of illicit activities, it serves various purposes, from privacy protection to political activism. Understanding how to access the dark web safely can empower individuals to navigate this hidden realm responsibly.
Acess Dark Web
Before diving into the intricacies of the dark web, it is essential to understand what it is and why individuals might want to access it.
What is the Dark Web?
The dark web is a network of encrypted websites that require specific software to access. The most common method is using the Tor browser, designed to anonymize users’ online activities. It operates alongside the surface web (the part of the internet most people know) and the deep web (websites not indexed by standard search engines).
- They often provide access to vast amounts of compromised data from previous hacks or breaches.
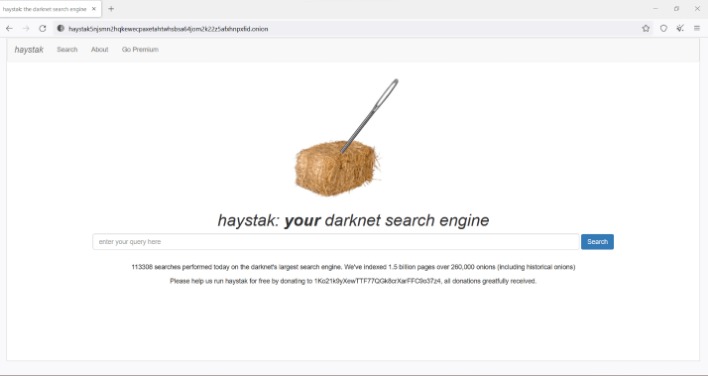
- Dark web websites won’t show up on Google, but they are indexed by dark web search engines such as Torch.
- Safe access ensures that research, investigation, or monitoring does not turn into accidental compromise.
- It is commonly used for private communications and is a haven for illegal activity.
- Enable access to hybrid networks and devices globally.
- The darknet is the infrastructure, and the dark web is the content that is accessible through that infrastructure.
Reasons to Access the Dark Web
- Privacy: Individuals seeking to protect their identities and personal information.
- Activism: Whistleblowers and journalists in oppressive regimes may use it to communicate safely.
- Research: Scholars may explore topics often hidden from public view.
How to Access the Dark Web Safely
Engaging with the dark web requires caution. Here’s a step-by-step guide:
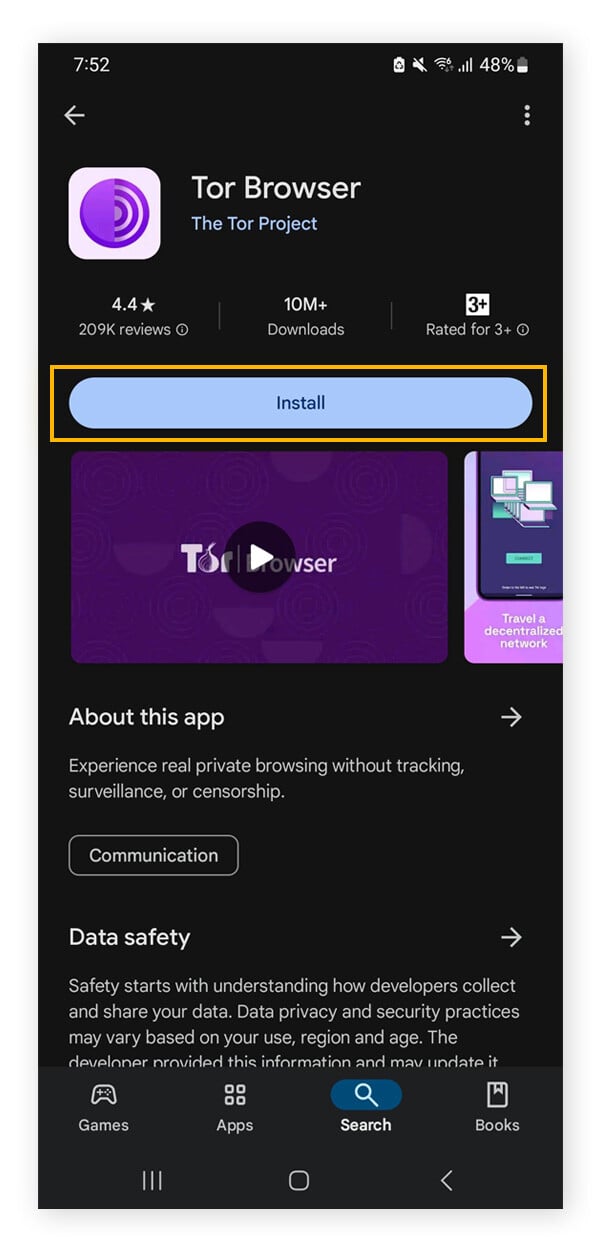
- Download the Tor Browser: This browser is designed for accessing .onion sites on the dark web.
- Use a VPN: A Virtual Private Network adds an additional layer of security and anonymity.
- Stay Secure: Enable security settings in the Tor browser and avoid sharing personal information.
- Access Trusted Sites: Start with well-known sites and forums to gain experience.
- Be Cautious: Avoid downloading files or clicking on unknown links.
Understanding the Risks
While the dark web can provide anonymity, it is not without risks. Users may encounter:
- Illegal Activities: Many illicit services operate here, and involvement can lead to legal issues.
- Scams: Many websites are fraudulent, aimed at stealing information or money.
- Malware: Downloading files can expose devices to harmful software.
FAQs About Accessing the Dark Web
Is accessing the dark web illegal?
Accessing the dark web itself is not illegal; however, participating in illegal activities on it is.
Do I need special software to access the dark web?
Yes, the Tor browser is the primary method for accessing sites on the dark web.
Can I remain completely anonymous on the dark web?
No online activity is entirely anonymous, but using tools like Tor and a VPN enhances your privacy.
Conclusion
Accessing the dark web can be a valuable tool for those seeking privacy and security. However, users must navigate this space wisely and be aware of the potential dangers. By following safe practices and remaining informed, individuals can explore this hidden corner of the internet responsibly.