These links are made up of a string of random characters, and they end in the top-level domain “.onion” instead of “.com” or “.org.” The Tor browser allows you to access any website, but it only works if the site has an address that ends in “onion”. It has top security features to keep your information fully private, great speeds to counter slow loading pages, and a global server network so you can use it in most countries.
- Tor Metrics is the go-to hub for stats and insights on the Tor network.
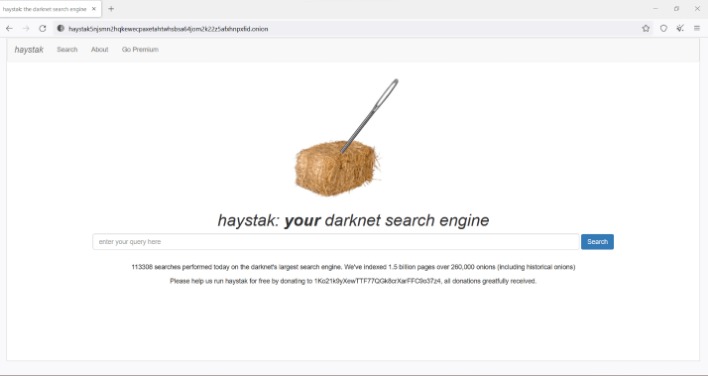
- Learn which dark web search engines reveal real, actionable insights.
- Torch is one of the oldest and largest dark web search engines.
- A second-pass research flow benefits most, especially after core entities and terms are already identified.
- Plus, many .onion websites are created to be temporary or invite-only, so they may not even be active long enough to be indexed.
- Unlike Google’s web crawlers that follow links all over the public internet, dark web search engines use Tor based crawlers and sometimes user submissions to discover hidden sites.
Keybase also offers extremely user-friendly secure chat and file-sharing services through its app. It publishes a newsletter in multiple languages and not only runs onion services for its website but all its email and chat services. Wasabi Wallet is a Bitcoin wallet that not only hides all your data in the Tor network but also allows you to "join" your transactions with others to increase your anonymity. While its .onion address doesn’t make it much easier to maintain an anonymous account, it does make Facebook more accessible in places where it’s censored. To make its journalism more accessible to readers around the world, the New York Times launched its onion service in 2017. Founded in 2012, it stores snapshots of websites, making it possible to “go back in time” and see what websites used to look like and what information they contained.
The internet has long been an essential part of our lives, serving as a platform for communication, entertainment, and information. However, not all parts of the internet are easily accessible or visible to the average user. One such area is the realm of .onion links, which provides anonymity and privacy for users and websites alike. Understanding how these links work and their significance can empower individuals navigating the digital landscape.
.onion Links
.onion links are special URLs that can only be accessed through the Tor network, a system designed to enable anonymous communication and browsing. These links are often associated with websites that prioritize privacy and security, making them appealing for various users, from whistleblowers to privacy advocates.
How Do .onion Links Work?
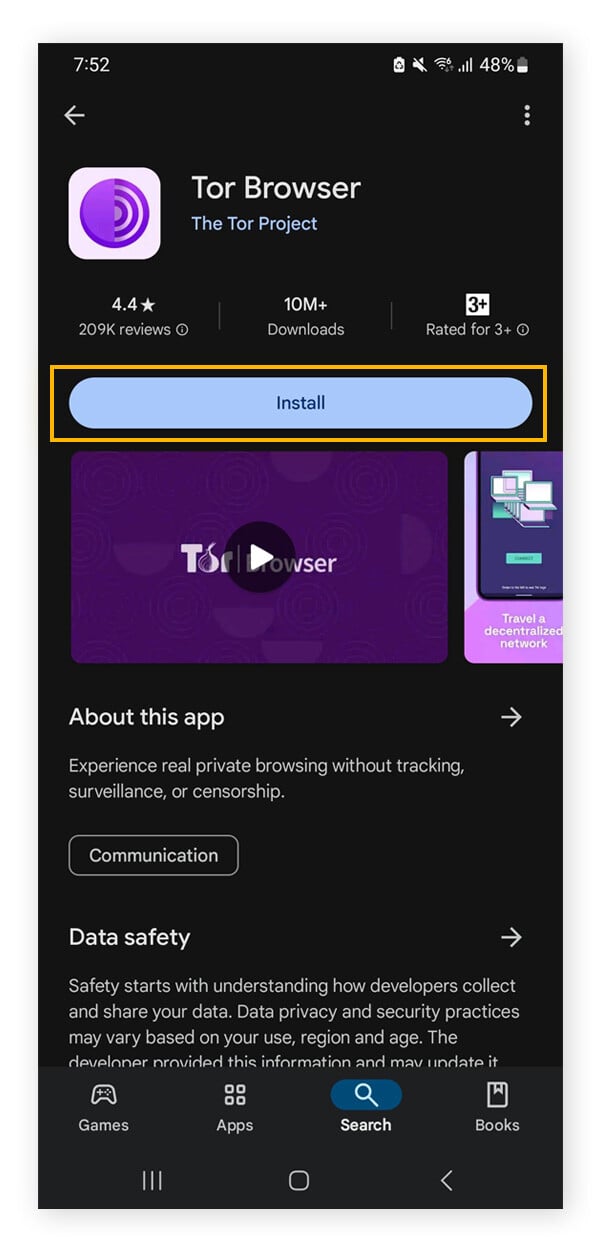
Accessing a .onion link requires a specific browser called the Tor Browser. This browser uses several layers of encryption to obscure users' locations and online activities. Here's how it works:
- Routing through nodes: When a user connects through Tor, their internet traffic is routed through a series of volunteer-operated servers, known as nodes. Each node only knows the location of the previous and next nodes, ensuring anonymity.
- Entry, middle, and exit nodes: The process begins at an entry node, passes through multiple middle nodes, and often concludes at an exit node. While traditional browsers connect directly to websites, Tor obscures the user's pathway.
- Accessing .onion domains: The final destination for a Tor user is a .onion link which exists solely on the Tor network. These addresses are not indexed by standard search engines, adding an extra layer of confidentiality.
Why Use .onion Links?
There are several reasons why individuals or organizations may seek to access .onion links:
- Privacy: Users may wish to browse the internet without fear of surveillance or data collection.
- Freedom of expression: Activists and journalists in oppressive regimes can communicate and share information without being tracked.
- Secure communication: Whistleblowers can share sensitive information with journalists without revealing their identities.
- Information on sensitive topics: Those seeking information on taboo issues may find specialized content only available through .onion links.
Risks and Considerations

While .onion links provide several advantages, they are not without risks:
- Illegal content: Some .onion sites may host illegal activities like drug trafficking or illicit services, which could compromise users.
- Scams: The anonymity of the network can attract scammers, posing risks to users seeking legitimate services.
- Malware: Some websites on the dark web may contain harmful software that can infect users' devices.
Frequently Asked Questions (FAQs)
- Can anyone access .onion links? Yes, but it requires the Tor Browser for secure access.
- Are .onion sites illegal? Not all are illegal; many serve legitimate purposes, but caution is advised.
- Is my identity safe while using Tor? While Tor provides privacy, it is not foolproof. Users should take additional precautions.
Understanding .onion links and the Tor network serves as a vital resource for those seeking privacy and security in their online activities. By arming themselves with knowledge, individuals can navigate the complex web of the internet more safely and informed, recognizing both the benefits and potential pitfalls of engaging with this hidden part of the digital world.