In the ever-evolving digital landscape, cybersecurity threats continuously emerge, posing risks to individuals and organizations alike. One particular area of concern is the realm of vulnerabilities known as 0day onion. This term refers to a significant security flaw that can be exploited before it is known to the software vendor or the public, making it a critical concept in understanding the need for robust cybersecurity measures. In this article, we will explore what 0day onion vulnerabilities are, their implications, and how individuals can protect themselves against such threats.
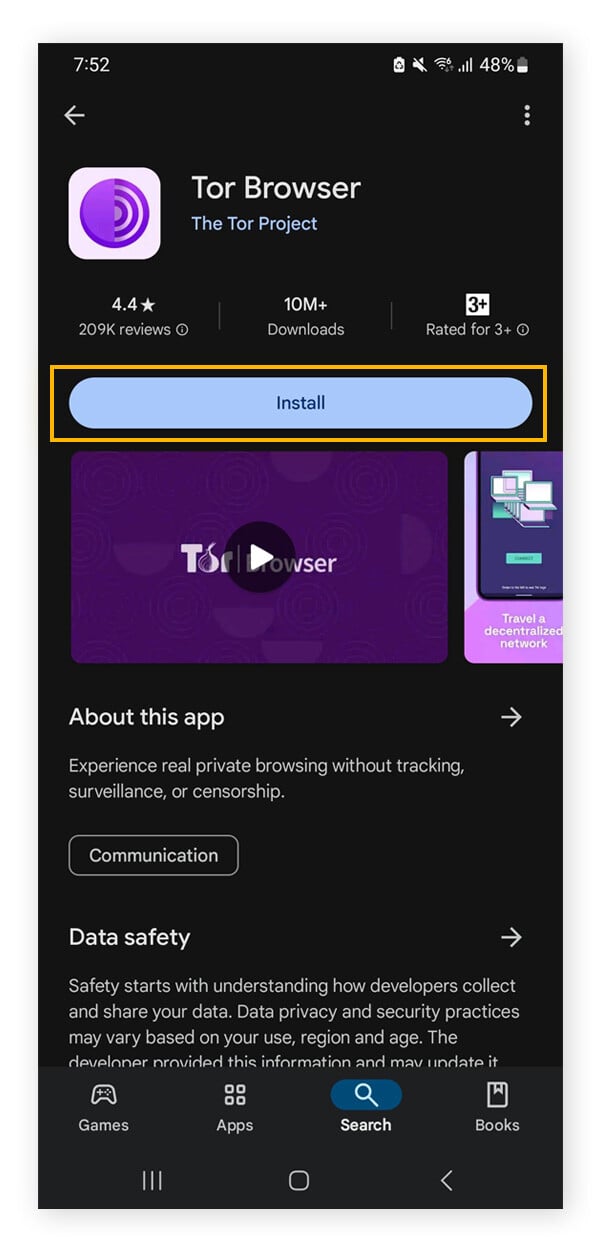
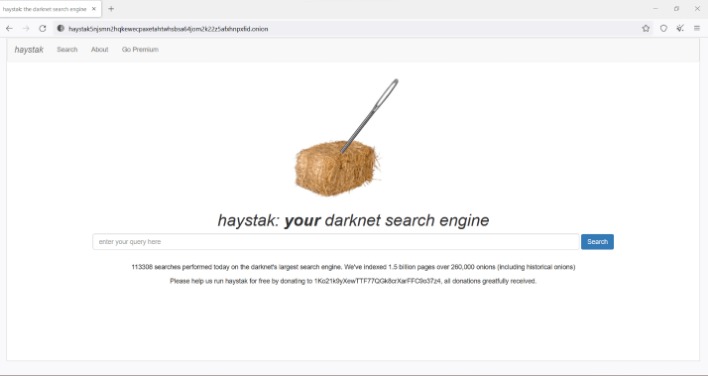
As governments and organizations implement more robust cybersecurity measures, the methods employed by hackers may evolve, compelling them to find new ways to maintain anonymity while conducting their operations. Stricter laws could lead to heightened penalties for those caught trafficking in exploit kits or data obtained through these vulnerabilities, potentially driving such activities further underground. These vulnerabilities can be extremely lucrative on the black market, often selling for thousands of dollars to malicious actors seeking to exploit them for malware deployment and other nefarious purposes. Learning about these patterns will not only inform defensive strategies but also highlight the importance of proactive vulnerability management in maintaining cybersecurity. The Tor network serves as a vital tool for those involved in the distribution and sale of 0day vulnerabilities. The Future of 0day Onion holds a complex position in the realms of cybersecurity and the underground black market.
Its website features security research publications and a searchable CVE database. Vidalia onions are Yellow Granex onions that were grown in the low-sulfur soils of Vidalia, Georgia. The thick-skinned bulbs have an excellent storage life and are quite flavorful raw or cooked.
- The existence of a 0day onion undermines the foundational trust in these anonymized networks, potentially revealing sensitive user data and operational details.
- You can withdraw your consent and stop sharing this data anytime by clicking “Cookie Consent” at the bottom of Opera’s webpage.
- The breach fundamentally destroys the integrity of the service, as users can no longer trust that their interactions are confidential or that the operator is who they claim to be.
- Additionally, 0day Onion services often leverage hidden service architecture, allowing them to remain cloaked and resilient against takedown attempts.
What is a 0day Vulnerability?
A 0day onion vulnerability is a security flaw in software that is exploited by attackers before the developer has a chance to address it. The term "0day" signifies that the vulnerability is known to the public and attackers "zero days" into the software's existence, giving them a window of opportunity to exploit it without any available fix. The term "onion" is often used in the context of layered security measures that can help protect against such vulnerabilities.
These hidden services act as volatile marketplaces where undisclosed software vulnerabilities are traded as commodities, often before developers are even aware a flaw exists. This underscores the sobering reality that anonymity networks are not magic; they are complex systems built on code, and where there is code, there can be exploitable bugs with severe consequences for user security. These undisclosed flaws, hidden within the network’s complex layers of encryption and routing, can compromise the anonymity of entire services or user populations before a patch is even conceivable. In the clandestine digital economy, an initial access broker may purchase the exploit or the access it provides, specializing in compromising target networks and then selling that foothold to other threat actors, such as ransomware groups.
How Does 0day Onion Work?
Understanding how 0day onion vulnerabilities function can help users safeguard their information. Here’s how it typically unfolds:
- Discovery: A hacker discovers a vulnerability in a widely used application or system.
- Exploit Development: The hacker develops an exploit that takes advantage of the flaw.
- Execution: The exploit is launched against a target before the software vendor can release a patch.
- Consequences: The attack can lead to data breaches, system compromises, or unauthorized access to sensitive information.
Implications of 0day Onion Vulnerabilities
The impact of 0day onion vulnerabilities can be severe. Here are some key implications:
- Data Breaches: Sensitive information can be stolen, leading to identity theft and financial loss.
- Infrastructure Damage: Critical systems can be compromised, affecting personal safety and operational continuity.
- Reputation Damage: Companies can suffer reputational harm, leading to loss of customer trust and revenue.
- Legal Consequences: Organizations may face legal repercussions if they fail to protect user data adequately.

Protecting Yourself Against 0day Onion Vulnerabilities
While it is impossible to prevent all 0day onion vulnerabilities, there are several proactive measures individuals and organizations can take to mitigate risks:
- Regular Updates: Keep software and systems updated to patch known vulnerabilities.
- Use Antivirus Software: Employ robust antivirus and anti-malware solutions that offer real-time protection.
- Implement Firewalls: Utilize firewalls to restrict unauthorized access to your network.
- Educate Users: Train individuals on recognizing phishing attempts and other social engineering tactics.
FAQs about 0day Onion
Here are some frequently asked questions concerning 0day onion vulnerabilities:
- What is the origin of the term "0day"?
It refers to the fact that the vulnerability is exploited on the same day it becomes known to attackers. - Are all software vulnerable to 0day attacks?
Yes, any software can have vulnerabilities, highlighting the importance of ongoing security measures. - Can individuals report 0day vulnerabilities?
Yes, there are ethical channels available for reporting vulnerabilities to software vendors.
In conclusion, being informed about 0day onion vulnerabilities is crucial for protecting oneself in a digital world rife with threats. By understanding how these vulnerabilities operate and implementing appropriate security measures, individuals can significantly reduce their risk of becoming victims of cybercrime.